What is MPC Wallet? Brief Guide to Multi-Party Computation

In the realm of digital assets, trust and security are more than just words; they underpin the entire experience. At the heart of a mpc wallet are key management and security, which change the game for control and transaction authorization. Instead of one place storing a private key, the power is disbursed with multi-party computation, or MPC, across multiple parties.
Here’s what’s exciting: the global digital asset custody market was estimated to be about US $683.4 billion in 2024, with forecasts projecting an uptick to US $4,378.8 billion by 2033, fueled in large part by innovations such as MPC wallets.
As more institutions and businesses engage with crypto and tokenized assets, they will be looking for a more sophisticated approach for holding and moving value. An mpc wallet does not just maintain a simple improvement; it potentially turns the existing notions of custody, control, and risk on their heads.
In the following guide, you will have a well-thought-out guide to what a mpc wallet is, how it works, where it is used, and why it might matter to you – whether you are managing a handful of coins or managing a substantial digital treasury.
- An mpc wallet uses multi-party computation to secure digital assets by splitting private keys into multiple encrypted parts.
- It removes single points of failure and enables shared transaction authorization among trusted participants.
- MPC wallets are used by individuals, enterprises, and institutions for secure, scalable, and compliant asset management.
- This technology is defining the trajectory for digital custody through enhanced security, flexibility and resilience.
- Multi-Party Computation (MPC) provides a means for multiple entities to accomplish cryptographic functions together without delivering their private data to each participant.
- The MPC wallet replaces the single private key model with distributed keys stored on different devices and/or users.
- MPC wallets are utilized in institutional asset management, DeFi activities, corporate treasury and self-custody on the individual level.
- Benefits of MPC wallets are additional security on top of the multisig of hardware devices, no single point of failure, flexible access control through decentralized keys, simple key management, and scalability.
- Challenges include high development cost, complexity of implementation, recovery difficulty, and lack of standardized approaches across various platforms.
- The wallet can be divided into four fundamental types: single-user (individual), multi-user, custodial and hybrid models based on user needs for security and operation.
- Some notable examples of MPC wallets are ZenGo, OKX Wallet, Coinbase Wallet, Fireblocks and Safeheron, all of which showcase their unique benefits and use cases.
- MPC wallets are changing the landscape for digital asset security by combining security through cryptographic innovation and usability for personal use or enterprise use.
What is Multi-Party Computation (MPC)
Multi-Party Computation, which is short for MPC is a cryptographic technique that permits a group of people to get a result without exposing their personal data to one another. It allows many users to be involved in a specific activity and, at the same time, keep their contributions secret from the others.
Think about a scenario where a group of individuals wants to know the average of their salaries but no one is willing to disclose the actual amount. The use of MPC technology enables this to be done by means of very complicated mathematical protocols, which not only safeguard each person’s data but also return the correct result. No participant’s input is exposed and yet the group gets the result required.
This is one of the applications that are widely adopted in blockchain and digital security. In the case of crypto wallets, MPC is a solution that guarantees that no one person or device can have access to the entire private key. Rather, the key is divided into encrypted segments that are then allocated to different parties or devices. Only when these segments come together to verify the transaction can it be executed.
This gives rise to a system that is both private and secure. A hacker will not be able to gain full access to the key or the currency it secures even if he manages to take over one part of it. MPC has been a huge leap in the field of cryptography and is the core of the digital Mpc wallet.
What is an MPC Wallet
An mpc wallet represents a digital wallet that secures and manages private keys through the multi-party computation method. Instead of one location keeping a single private key, the wallet breaks it down into several encrypted parts with the name key shares. Oftentimes these shares are put on different devices or are held by different individuals, and they all together are the ones who can authorize transactions without revealing or reconstructing the full key at any point in time.
This setup eliminates the single point of failure in traditional wallets. In a usual crypto wallet, the one who gains access to the private key can control the funds. On the contrary, in an mpc wallet, no one person or device has total access, which makes unauthorized entry much harder.
MPC wallets are appropriate for both private individuals and enterprises that prioritize security, flexibility, and shared control. They enable several participants to give their approval for the transactions collectively; that is why they are convenient for exchanges, trade, and institutions managing huge digital portfolios.
An mpc wallet integrates cutting-edge cryptographic security with intuitive usability; thus, it offers a safe and efficient method for digital asset management in an ever more decentralized financial environment.
Also Check: Top Cold Crypto Wallets: Ultimate Security Guide
How Does an MPC Wallet Work
The mpc wallet is a type of wallet that uses a distributed cryptographic way of processing instead of a single private key. It relies on multi-party computation to break the key into several encrypted parts, which are distributed to different devices or servers and called key shares. These parts never come together in one place and thus provide stronger protection against theft or compromise.
Here’s how the process works:
- Key Generation: The mpc wallet generates multiple key shares instead of one private key. Each share is an individual part of the complete cryptographic key.
- Key Distribution: The key shares are either stored on various devices or servers or administered by different people. No one has the private key of the wallet; thus, no one has total access to it.
- Transaction Initiation: Once a user initiates a transaction, the wallet starts a secure computation involving all key shares. Every share partakes in the signing of the transaction without letting its part be disclosed.
- Secure Computation: The key shares carry out encrypted arithmetic operations. The system generates a legitimate digital signature collectively without reconstructing the entire private key.
- Transaction Approval: When the signature is verified, the transaction is sent to the blockchain. The whole process takes place in seconds and privacy is maintained throughout.
- Ongoing Security: Even if one key share or device is hacked, the hacker cannot access the complete key or make independent transactions.
An mpc wallet is a combination of privacy, decentralization, and shared authorization; it forms a trusted infrastructure for secure digital asset management.
Steps to Develop an MPC Wallet
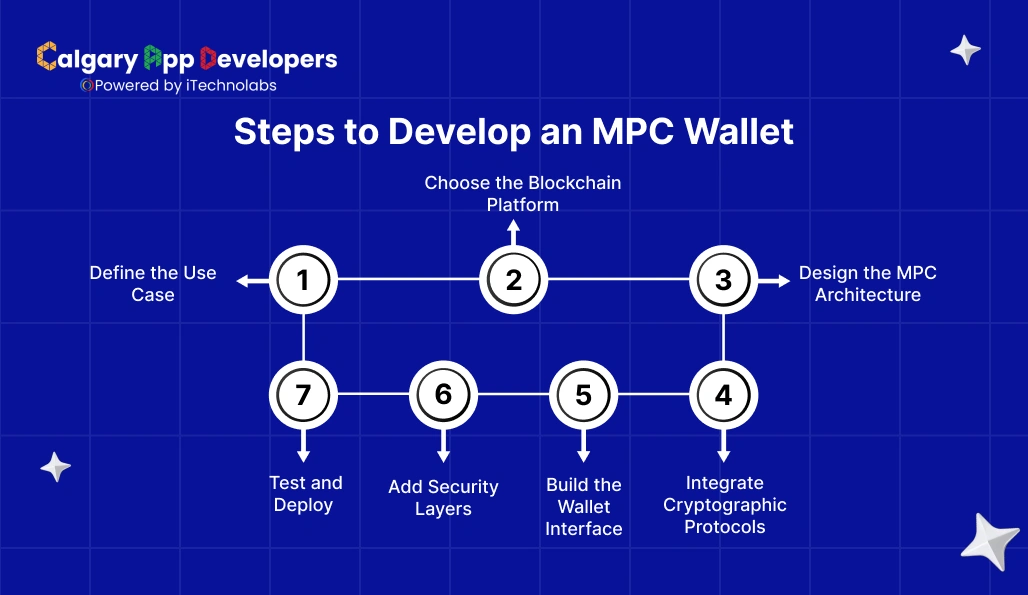
The process of mpc wallet development is quite elaborate and security-oriented, incorporating a mix of cryptography, blockchain integration, and user experience design. There is no doubt that this combination offers a solid ground for a product that is secure, scalable, and trustworthy.
Here’s a detailed breakdown of each step:
- Define the Use Case
Before any code is written, the primary purpose of the wallet is to be identified first.
- The wallet is to be aimed either at individual users, enterprise clients, or institutional investors. All these categories have unique demands regarding compliance and security.
- Likewise, the types of assets that the wallet will support need to be determined, which may be cryptocurrencies, stablecoins, or tokenized assets.
- Furthermore, the frequency and types of transactions, user roles, and authorization levels must be stated, as these will aid in the development of the security model.
- Finally, regulatory requirements should be defined at the very beginning, especially if the wallet will be working with KYC, AML, or financial custody standards.
- Choose the Blockchain Platform
The blockchain that is selected dictates transaction logic, expense, and interoperability.
- While Ethereum is the go-to blockchain for DeFi and smart contracts, Bitcoin is perfect for simple custody solutions.
- If the wallet is to be multi-chain compatible, then the support for assets from several blockchains must be the first consideration.
- The blockchain’s security, speed, and transaction fees need to be weighed up and compared before integration.
- Plus, the network should be one where APIs or SDKs that are suitable for cryptographic operations are provided, especially those that are MPC-friendly.
- Design the MPC Architecture
The architecture will be the one to describe how the keys will be generated, stored, and used in the signing of the transactions.
- One way of doing this is by using key sharding, which is where a private key is divided into several encrypted shares.
- To counter single-point failure, it is necessary that each share be assigned to a separate device, server, or participant.
- A threshold model like 2-out-of-3 or 3-out-of-5 can be developed to determine the number of shares that are needed for a transaction to be approved.
- Include redundancy plans for backup and recovery without exposing key fragments.
- Integrate Cryptographic Protocols
Mpc wallets are highly dependent upon strong cryptographic foundations.
- Employ cryptographic techniques to validate the transactions only when a certain number of shares are involved.
- Introducing secure computation protocols like GG18, GG20, or their subsequent versions that opt to keep privacy if needed during distributed signing.
- Adding zero-knowledge proofs where needed to allow asserting of correctness without compromising on revealing critical information.
- Follow the strands of well-reviewed open-source libraries for implementation as a way of being transparent and reliable.
- Build the Wallet Interface
Even in security, the system has to be simple enough for daily use.
- Develop a user-friendly interface that easily shows complex operations.
- Provision of dashboards for portfolio monitoring, transaction history, and team permissions.
- Responsiveness is a must for web, mobile, and desktop applications.
- Add-on biometric authentication or PIN-based access for additional user security.
- Add Security Layers
When it comes to protection, every layer is of paramount importance and more so with digital assets.
- The first line of defense will be the deployment of multi-factor authentication and the use of device whitelisting to effectively eliminate unauthorized logins.
- Come up with a plan for the use of either secure enclave technology or hardware security modules (HSMs) for the safe keeping of the key shares.
- Penetration testing and audits of the system by third parties should occur regularly to spot weaknesses.
- The implementation of real-time monitoring and alert systems that check for suspicious activities should never be allowed to lapse.
- Test and Deploy
Testing of every component is to be done thoroughly before the entire programming launch.
- Perform unit testing on every cryptographic function, then do integration testing on wallet workflows.
- Use the method of stress testing to determine the system’s performance when it is under the burden of a heavy load.
- Carry out the simulation of possible attack scenarios, such as key leakage or the usage of compromised devices, to verify the resilience of the system.
- Once stability and compliance are confirmed, deploy the wallet and establish a routine for updates and security patches.
Developing an mpc wallet is a multidisciplinary process that merges cryptography, blockchain architecture, and user-centered design. A well-built wallet not only protects assets but also instills confidence in users who rely on secure digital infrastructure for daily transactions.
How Do MPC Wallets Ensure Security
An mpc wallet protects your digital assets by using sophisticated encryption, distributed key control, and access control. Instead of generating and storing a single private key in one place, the wallet breaks the key down into many encrypted pieces, called key shares. These key shares are spread across a number of devices or persons so that it is infeasible for a single breach or incident to provide a hacker access to the entire key.
Here are the main security mechanisms that make an mpc wallet difficult to compromise:
- Distributed Key Management: The wallet’s private key is never created or stored in its entirety. The key shares work together to sign each transaction. Without the entire key, accessing the funds is impossible, even with control of a rogue device.
- Threshold Authorization: MPC operates under a threshold model (2-of-3 shares or 3-of-5 shares, for example), meaning that a certain number of key shares must be involved in the signing of the transaction to make it valid. Therefore, an attacker’s only method to gain access to the funds in a wallet containing key shares would be to compromise multiple independent key shares simultaneously.
- Secure Computation Process: When a transaction is initiated, each key share processes its portion of the computation independently. The mpc wallet then takes the output of each of those computations and puts together a valid signature, without reconstructing the private key. This means the key itself is not revealed throughout the computation.
- Elimination of Single Point of Failure: Traditional wallets store the private key in its entirety. This creates a single point of failure where if the key is compromised, the asset is lost or stolen. The mpc wallet system does not have a whole key in one place, so an attack on one system or human error does not result in total loss or theft.
- Protection Against the Insider Threat: The system’s design will not allow a single employee or administrator to independently move assets to another account, as multiple members within the organization need to take part in the signature process. By having shared responsibility in the transaction process, this naturally reduces the internal security concern.
- Hardware and Software Safeguards: Many mpc wallets use secure enclaves, hardware security modules, and end-to-end encryption to store and process key shares. These technologies protect against malware, phishing, and unauthorized physical access.
- Continuous Verification and Audit: Regularly scheduled integrity checks, encryption upgrades, and audit trails will identify suspicious activity sooner than later. There are also monitoring tools that track key shares and requests for transactions requiring signatures for key shares to provide more transparency during the compliance requirements.
An mpc wallet reduces risk and provides operational control by leveraging distributed cryptography and layered security practices. It offers a high level of protection without sacrificing ease of use, making it one of the most trusted options for managing digital assets in today’s environment.
Also Read: Blockchain Wallet Development: An Ultimate Guide
Advantages of MPC Wallets
An mpc wallet offers several security and operational benefits that make it a preferred choice for managing digital assets. Its design focuses on eliminating single points of failure, enhancing control, and simplifying secure collaboration.
Here are the main advantages of using an mpc wallet:
- Enhanced Security
The private key never resides or is revealed in a single location. By separating it into encrypted key shares, an mpc wallet means that if one share gets breached, the entire key will remain secure.
- No Single Point of Failure
MPC-based wallets are based on a variety of private keys that can get lost, stolen, or compromised. MPC shares control among two or more parties or devices so that an entire breach is not possible through a single attack or error.
- Flexible Access Control
Businesses can set threshold rules such as 2-of-3 or 3-of-5 authorization to manage transactions securely. This allows shared decision-making while maintaining accountability and transparency among team members.
- Protection Against Insider Risks
Because no single individual has access to the private key, misuse within the organization is blocked. Members of staff or administrators can sign transactions only if the specified threshold is reached.
- Simplified Key Management
No complicated seed phrases or recovery keys need to be managed by the users. Key share generation and safekeeping are handled automatically by the mpc wallet, minimizing error and enhancing convenience.
- Multi-Device and Multi-User Support
Key sharing may be distributed between various devices or with multiple users. Such a design facilitates secure access from various points without sacrificing control as a whole.
- Scalability for Institutions
Large institutions with more than one account or asset can scale MPC-based systems with ease. The decentralized setup accommodates integration with established compliance, auditing, and governance controls.
- Resilience Against Phishing and Malware
Since the private key is never reconstructed, even advanced phishing or malware attacks cannot capture it during transactions. This makes mpc wallets stronger against common cybersecurity threats.
An mpc wallet provides the optimal balance of security, versatility, and performance. It is appropriate for individual investors who want strong security as well as institutions operating high-value digital assets that require strict protection.
Risks and Limitations of MPC Wallets
An mpc wallet provides advanced security, but several technical and operational risks must be considered. Below is a detailed look at each limitation.
- Complex Implementation
Building an mpc wallet involves advanced cryptographic protocols, secure computation models, and distributed key management. Each component must be designed with precision to prevent vulnerabilities. This level of complexity often requires dedicated cryptography experts and strong infrastructure, which makes the process time-consuming and difficult for smaller development teams.
- High Development Cost
MPC technology is capital-intensive to develop, test, and sustain. It needs top-class computational hardware, secure servers, and frequent third-party audits. Consequently, the overall development cost can be much greater compared to conventional wallet solutions. The costs also involve ongoing monitoring and updates for ensuring compliance and security standards.
- Limited Industry Standards
As opposed to traditional wallets, mpc wallet implementations do not have uniform global standards for encryption, key generation, and interoperability. Each developer can use varying approaches, and such divergence in methods can create compatibility problems when integrating with exchanges or third-party tools. Lacking uniform regulations can also complicate audits and cross-platform usage.
- Performance Overheads
The distributed requirement for MPC computations can slow down transaction processing. Every key share needs to exchange securely with other shares to produce a valid signature, and this adds lag. For companies that process thousands of transactions or are based on real-time trading, even small performance lags can affect operational efficiency and customer experience.
- Dependency on Secure Devices
Every key share in an mpc wallet needs to be secured on a trusted and secure device. If any of these devices is compromised or no longer available, signing transactions will be delayed. Physical and digital security must be ensured for all participating devices, particularly in enterprise settings with many users and locations.
- Recovery Complexity
Because no individual party has the entire private key, recovery is done through coordination of authorized participants. When one or more key shares are misplaced or compromised, recovery can be challenging and urgent. Mechanisms for effective recovery need to be established in order to restore access without revealing sensitive information or compromising system security.
- Limited User Awareness
Many users are unfamiliar with how multi-party computation works. The technical nature of setup and authorization may appear confusing to non-technical users. Without proper education, documentation, and guided onboarding, users might make errors that compromise efficiency or cause unnecessary delays in transaction approvals.
- Third-Party Dependency
Certain mpc wallets rely on third-party service providers to control computation nodes or handle partial key computations. It adds one more level of trust. The provider’s downtime, mismanagement, or security breaches can impact wallet functionality and transaction integrity. The providers need to be vetted and monitored for safety of operations.
Although an mpc wallet robustly increases digital asset security, these restrictions point to the significance of professional development, solid infrastructure, and education of users to provide long-term dependability.
Use Cases of MPC Wallets
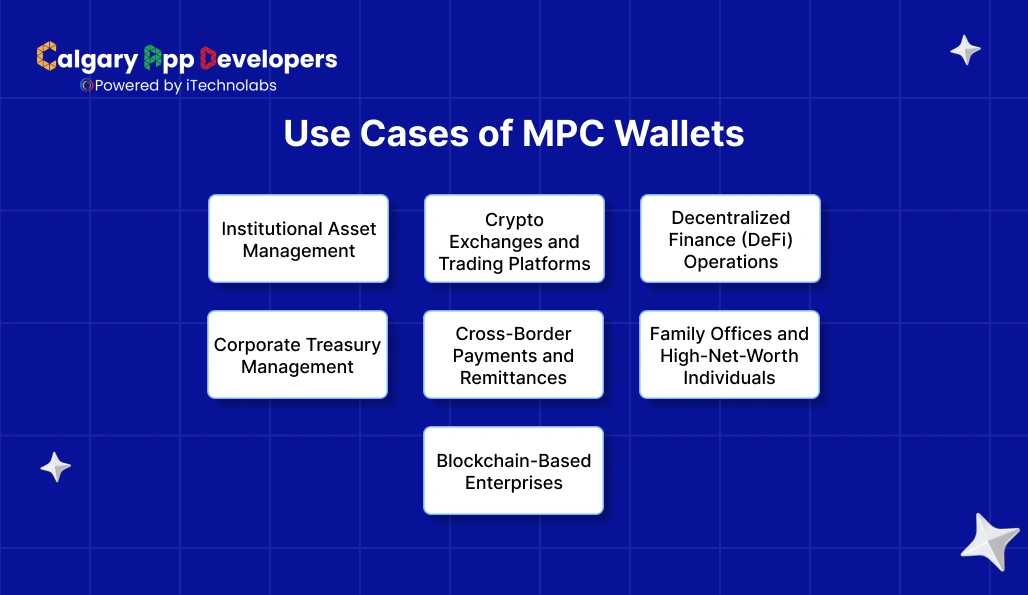
An mpc wallet provides versatility in personal, institutional, and enterprise use cases. Its distributed key mechanism makes it appropriate for organizations and individuals who need robust security, shared control, and regulatory compliance. Here are the most appropriate use cases where an mpc wallet provides obvious benefits.
- Institutional Asset Management
Financial institutions and cryptocurrency custodians utilize mpc wallets to safely manage large digital portfolios. The shared authorization model of the wallet ensures that one employee or system cannot move assets on their own. This eliminates insider threats and improves custody regulation compliance, positioning it well for banks, hedge funds, and investment companies dealing with digital assets.
- Crypto Exchanges and Trading Platforms
Exchanges tend to hold large amounts of assets for thousands of users. They can divide control of private keys among different systems or administrators using mpc wallets. This safeguards against unauthorized withdrawals and reduces loss in the event of a data breach. The technology also allows for quicker recovery when one node or system crashes.
- Decentralized Finance (DeFi) Operations
DeFi applications utilize mpc wallets to control liquidity pools and funds of smart contracts. The process of distributed signing requires that transactions and protocol updates be collectively approved by several trusted parties. Shared governance enhances transparency and increases the credibility of decentralized financial apps.
- Corporate Treasury Management
Businesses that keep crypto for payments, transactions, or investment purposes utilize mpc wallets to hold funds between departments. Authorized staff like CFOs, auditors, or compliance officers can be allocated each key share. The threshold signing model creates accountability and eliminates one-sided transfers, keeping financial control at all levels intact.
- Cross-Border Payments and Remittances
International trade businesses appreciate mpc wallets as they enable safe, multi-user management of large transfers. Global teams or regional offices can share key shares, allowing approved transactions to be made without centralizing sensitive data in one place.
- Family Offices and High-Net-Worth Individuals
Wealth management entities and private investors use mpc wallets to safeguard long-term crypto holdings. The multi-party setup allows trusted family members or advisors to share control, ensuring asset protection in the event of device loss, theft, or inheritance scenarios.
- Blockchain-Based Enterprises:
Startups and technology companies working in blockchain environments use mpc wallets to manage token distribution, payments, and salaries. The distributed control model makes auditing easy and offers an open audit trail for each transaction on the chain.
An mpc wallet covers a broad set of real-world applications, ranging from institutional custody solutions to individual asset protection. Its shared control and robust cryptography make it a secure instrument for contemporary digital finance.
Four Levels or Types of MPC Wallets
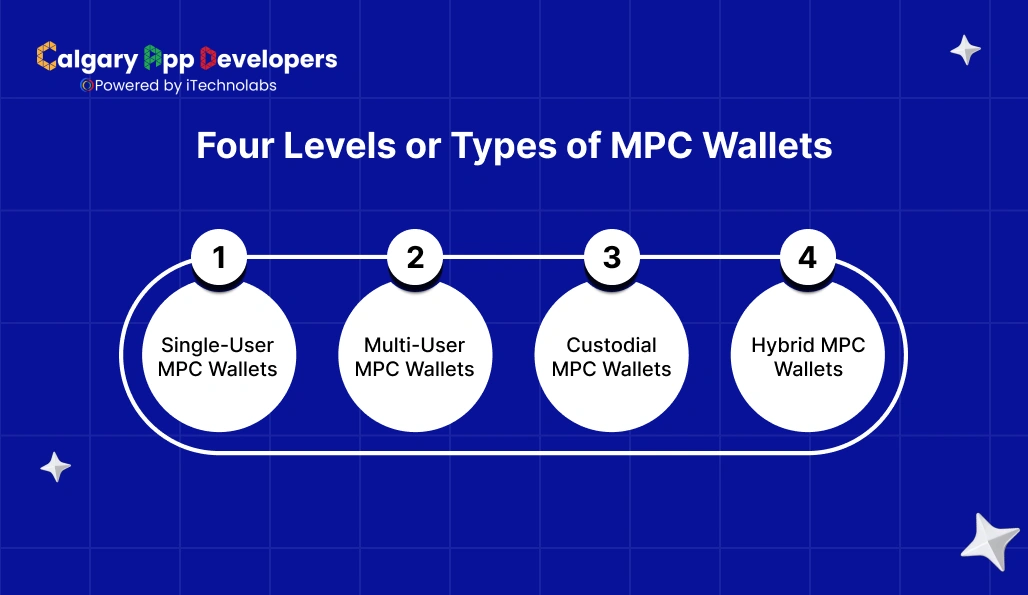
There are various implementations of MPC technology based on the desired level of security, control, and technical sophistication. Each mpc wallet type has a particular application and customer segment in mind, from individual users to big financial institutions. The knowledge of these different variations is necessary to select the appropriate model for particular business or individual requirements.
- Single-User MPC Wallets
This type of mpc wallet is designed for individual users who want enhanced security without managing complex setups. The wallet divides the private key into multiple encrypted shares stored across the user’s devices, such as a phone, laptop, or hardware wallet. Even if one device is compromised, the attacker cannot access the full key. Single-user MPC wallets are ideal for investors who value privacy and protection but prefer simple self-custody.
- Multi-User MPC Wallets
Multi-user mpc wallets are designed for organizations or groups where several users require governed access to digital assets. Each member owns a key share, and a transaction is only confirmed when a specified number of participants accept it. This shared responsibility model provides transparency, discourages abuse, and is well-suited for startups, exchanges, or funds where collective decision-making over transactions is necessary.
- Custodial MPC Wallets
Custodial mpc wallets are provided by third-party service providers who host key shares on behalf of customers. The user of the wallet has some degree of access and control, but the service provider is responsible for storage, upkeep, and recovery. This arrangement pairs institutional-grade security with simplicity of administration. It is popular among banks, regulated custodians, and enterprises that prefer to outsource crypto security to licensed service providers.
- Hybrid MPC Wallets
Hybrid mpc wallets combine elements of both custodial and non-custodial models. The user holds some key shares, while others are handled by a trusted provider. This model provides users with direct control over some of their security setup while enjoying expert monitoring and recovery assistance. Hybrid wallets suit businesses that desire to balance autonomy with operational convenience.
Each mpc wallet type has a distinct trade-off of security, control, and usability. Choosing the appropriate level is a function of factors like transaction volume, number of parties, risk tolerance, and technical ability.
Top MPC Wallet Examples
| Wallet | Launch Date | Launched By | Unique Selling Points (USPs) |
| ZenGo Wallet | Early 2020 (mobile) | ZenGo Ltd. | No seed phrases, mobile-first, beginner-friendly, zero hacks |
| OKX Wallet | (Date unspecified) | OKX Exchange | Multi-chain support, non-custodial MPC with advanced user options |
| Coinbase Wallet | (Date unspecified) | Coinbase Inc. | Trusted brand, wide chain support, self-custody with MPC option |
| Fireblocks Wallet | Sep 11 2023 | Fireblocks Inc. | Enterprise grade: MPC + policy engine + large-scale custody |
| Safeheron Wallet | (Date unspecified) | Safeheron | Open-source MPC, privacy & recovery focused, self-custody option |
- ZenGo Wallet
The wallet employs MPC technology to eliminate the use of seed phrases, providing a “keyless” self-custody experience. It splits the private key into mathematical shares such that only legitimate transactions are successful. The wallet is mobile-first and novice-friendly and features numerous assets and chains, and it has reported no hacks since its release.
- OKX Wallet
Built for non-custodial use with multi-chain support, OKX Wallet combines MPC security with users’ control. It is best for users who constantly interact with DeFi tokens on numerous chains and need high flexibility.
- Coinbase Wallet
While well-known for its general exchange, this wallet also accommodates an MPC-based self-custody solution, allowing users to store assets on many different chains with strong key management. It is appropriate for those with experience in the broader crypto space and who want security better than average.
- Fireblocks Wallet
With a focus on enterprise and institutional users, Fireblocks’ MPC wallet is geared for high-volume custody, trading desks and fintechs. It includes automated workflows, policy controls, MFA and MPC split key shares, making it a solid pro choice for serious digital asset activity.
- Safeheron Wallet
An open-source MPC wallet solution that prioritizes transparency and audibility. It accommodates individual and institutional usage with multi-factor authentication, sophisticated recovery features and a privacy focus. It is desirable to users who desire visibility of code and trust framework.
Conclusion
The advent of mpc wallet technology represents a significant leap in digital asset protection. Replacing the heritage single-key method with distributed cryptographic computation, MPC introduces a new standard of control and durability to wallet management. It enables users and organizations to jointly sanction transactions while keeping private keys safe at all times.
For retail investors, an mpc wallet provides reassurance with enhanced security and easier key management. For institutions, it represents a scalable infrastructure that addresses compliance, governance, and operational security needs.
With growing adoption of blockchain, the mpc wallet will be at the forefront of dictating how assets will be stored, moved, and protected. It creates the best of cryptography and cooperation, a platform for safe and future-proof digital finance.
FAQs:
1. Are MPC Wallets Safe?
Yes, mpc wallets are considered highly secure because they eliminate the need for a single private key. Instead, they divide the key into multiple encrypted shares stored across different devices or users. Transactions require participation from several authorized parties, making it nearly impossible for hackers or internal actors to gain full control of the assets.
2. How Does MPC Signing Work?
MPC signing uses distributed cryptographic computation. Each participant or device holding a key share performs an independent calculation on its part of the key without revealing it. These computations are combined to generate a valid digital signature that authorizes a transaction. The full private key is never reconstructed, keeping it safe from theft or exposure.
3. What Is the Cost of Developing MPC Wallets?
Developing an mpc wallet can cost between USD 80,000 and 250,000, depending on features, architecture, security standards, and supported blockchains. Enterprise-grade wallets with compliance tools, APIs, and multi-chain integration fall on the higher end. Costs also include audits, infrastructure setup, and continuous maintenance to ensure secure and compliant performance.
4. What Is the Difference Between a Multisig Wallet and an MPC Wallet?
A multisig wallet uses multiple blockchain-level signatures for transaction approval, with each signer holding a separate key. An mpc wallet, by contrast, splits one private key into multiple encrypted shares and performs distributed signing off-chain. MPC offers more flexibility, faster execution, and privacy since it avoids publishing multiple signers’ data on the blockchain.
5. What Is the Difference Between an MPC Wallet and a Hardware Wallet?
A hardware wallet stores a single private key securely in an offline device, protecting it from online threats. An mpc wallet removes the concept of one full key by splitting it across devices and participants. While hardware wallets rely on physical isolation, mpc wallets depend on distributed cryptography for continuous online yet secure operations.
6. What Kind of Wallet Are MPC Wallets?
MPC wallets are non-custodial cryptographic wallets that enable distributed key management. They fall under the category of self-custody wallets, where users retain control of their assets without relying on a centralized authority. By design, they combine institutional-grade security with the flexibility of personal control, making them suitable for both individuals and enterprises.
7. What Is Done When Another Party Holding the Private Key Is Unavailable?
MPC wallets use threshold cryptography, which means only a subset of key shares is required for authorization. For example, in a 3-of-5 setup, any three participants can sign a transaction. If one holder becomes unavailable, the remaining authorized parties can still approve transactions or initiate a secure recovery process using backup shares.
8. How to Switch from a Traditional Wallet to an MPC Wallet?
Migrating from a traditional wallet to an mpc wallet involves securely importing or regenerating private keys as distributed key shares. Users or organizations set up key shareholders, define authorization thresholds, and transfer existing assets to the new wallet address. Professional wallet providers often assist with migration and compliance verification for a seamless transition.
9. What Type of Blockchain Services Is It Offering?
An mpc wallet provides services centered on secure digital asset management, including transaction authorization, multi-user access control, custodial and non-custodial storage, compliance integration, and recovery solutions. Advanced implementations extend to DeFi operations, cross-chain transfers, and institutional treasury management while maintaining complete cryptographic protection of private keys.